
Banking smarter is easier than ever.
Unlock more benefits and rewards plus earn interest when you open a checking account.
Apply in minutes with just $25.
Access us wherever you go.
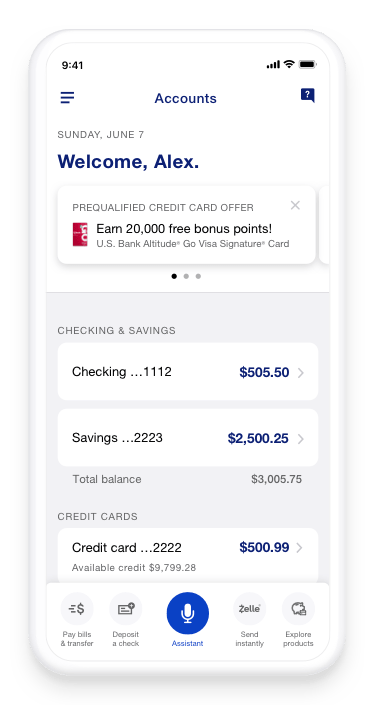
Bank from almost anywhere with the U.S. Bank Mobile App.
Borrowing money is a big deal. We’re ready to help.
From calculators and rate charts to get you started, to experienced loan officers and bankers, U.S. Bank has answers for all your loan and mortgage questions.
Home mortgage
Auto loan
Home equity line of credit
Happening now

Spring refresh
Five areas to clean that save you money

Planning ahead
Best home improvements to get the most ROI

Money matters
Extra cash? Here's how to use it wisely.
Start of disclosure content
Disclosures





